Intro
This post looks at creating and maintaining HTTPS/SSL/TLS Certificates for multiple WordPress sites running on the same host.
Some background…
This website is one of several different domains/sites/blogs hosted on my single Google Cloud server, with one public IP address shared for all websites. I’m using WordPress Multisite to do this, based on a very well put together Appliance provided by Bitnami.
WordPress Multisite allows me to cheaply, easily and efficiently serve multiple sites from the one host and IP address, sharing the same host resources (CPU, Mem, Disk) which is great but makes seting up HTTPS/SSL Certificates a little different to the norm – the same cert has to validate multiple sites in multiple domains.
I’d banged my head against this for a while and looked at many different tools and tech (some of which are mentioned below) to try and sort this out previously, but finally settled on the following process which works very well for my situation.
There is some good info on why you may want SSL/TLS certificate for your website(s), background info and some popular providers reviewed: https://makeawebsitehub.com/free-ssl-tls-certificate/
“WordPress is the world’s most popular blogging and content management platform. With WordPress Multisite, conserve resources by managing multiple blogs and websites from the same server and interface.”
CERT PROVIDER
Let’s Encrypt is a free, automated, and open Certificate Authority created by the Linux Foundation in collaboration with the Internet Security Research Group. There are many other certificate providers available, but I’m using this one.
LEGO – the Let’s Encrypt Go Client
Here’s the high level plan:
- Install the Lego client – see Step 1 here
- Generate a Let’s Encrypt certificate for your domain
- Configure the Web server to use the Let’s Encrypt certificate – see Apache or Nginx options on Bitnami site
- Add a cron job to run every <90 days
I used this excellent Bitnami article to work through the process, it explains the steps in greater detail:
https://docs.bitnami.com/aws/how-to/generate-install-lets-encrypt-ssl/
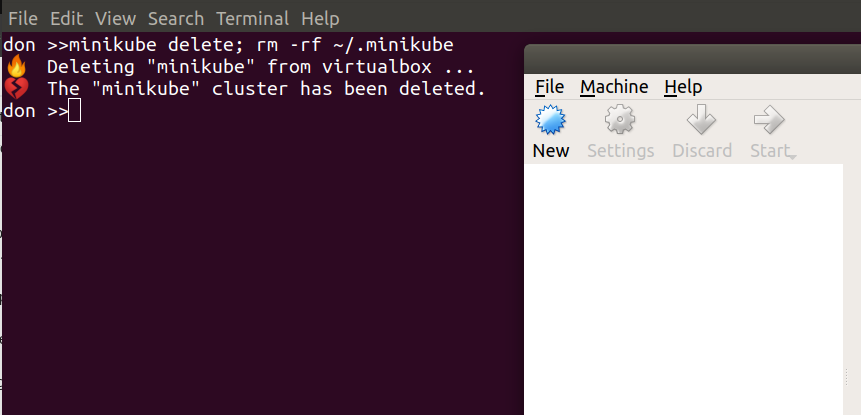
Stop services
sudo /opt/bitnami/ctlscript.sh stop
Get/renew certificates
Once lego is set up, you can request multiple certs like this – just make sure to change the --domains="whatever" entries and add as many as you need. Remember all of your sub domains (www. etc) too.
sudo lego --tls --email="my@email.com"--domains="donaldsimpson.co.uk" --domains="www.donaldsimpson.co.uk" --domains="www.someothersite.com" --domains="someothersite.com" --path="/etc/lego" run
Noe you’ve got the certs, move them in to place and chmod them etc:
sudo mv /opt/bitnami/apache2/conf/server.crt /opt/bitnami/apache2/conf/server.crt.old
sudo mv /opt/bitnami/apache2/conf/server.key /opt/bitnami/apache2/conf/server.key.old
sudo mv /opt/bitnami/apache2/conf/server.csr /opt/bitnami/apache2/conf/server.csr.old
sudo ln -sf /opt/bitnami/letsencrypt/certificates/DOMAIN.key /opt/bitnami/apache2/conf/server.key
sudo ln -sf /opt/bitnami/letsencrypt/certificates/DOMAIN.crt /opt/bitnami/apache2/conf/server.crt
sudo chown root:root /opt/bitnami/apache2/conf/server*
sudo chmod 600 /opt/bitnami/apache2/conf/server*
Restart services
sudo /opt/bitnami/ctlscript.sh start
PLUGIN – JSM’s Force SSL / HTTPS
By this point I was happy that the nice new HTTPS certs were finally working reliably for all of my sites, but was aware that Google and external links would still try to get in through HTTP URLs.
After trying a few WordPress plugins that sounded like they should correct this neatly for me, I settled on JSM’s Force SSL/HTTPS plugin. As the name suggested, it quickly and easily redirects all incoming HTTP requests to HTTPS. It was simple to install and setup and works very well with WordPress Multisite too – thanks very much JSM!
CRONJOB
Now that the process works, the certificates need updated every 90 days which would be a bit of a pain to remember and do, so adding a simple script to a cron job saves some hassle.
OTHER OPTIONS and things I found interesting…
Many other clients are available, there’s a large list here:
https://letsencrypt.org/docs/client-options/
One of the more popular is Certbot: https://certbot.eff.org/
Tech links
SNI – Server Name Indication:
https://www.digicert.com/ssl-support/apache-multiple-ssl-certificates-using-sni.htm
SAN – Subject Alternative Name:
https://www.digicert.com/subject-alternative-name.htm